- Limits of Landlines and Mobile Networks
- Zadarma’s Security Features
- 2FA authentication
- TLS and SRTP encryption
- Restriction by IP
- Virtual Numbers for privacy protection
- Control access to your Virtual Numbers and calls
- Automatic email alerts
- Automatic blocking for suspicious call activity
- eSIM for secure and reliable internet connection
- 24/7 Customer and Technical support
Trusting new technological solutions for traditional services we’re accustomed to may not be easy. Even if these innovations offer clear advantages. VoIP (Voice over Internet Protocol) is not entirely new to the market. It has grown over the past few years, which can make it feel relatively new to some users.
In this article, we’ll explore the security strengths that VoIP offers in comparison to traditional telephony.
Limits of Landlines and Mobile Networks
Traditional landlines and mobile networks were developed before cybersecurity became a priority. Mobile carriers have added security features over time, but they still don’t match what VoIP can offer.
Landlines
- No Encryption: Most landline calls are transmitted in analog form. It makes them easy to intercept with physical access.
- Wiretapping Risks: Anyone with access to the lines can listen in without detection.
- No Control or Logging: You can’t see who tried to access your line or when.
Mobiles
- Weak or Outdated Encryption: GSM encryption is outdated, and in many cases, it can be cracked in real time.
- Limited Control Over Security: With traditional mobile networks, you're fully dependent on your carrier’s infrastructure and security practices, with little control in how your data is protected.
- Potential Exposure of data: Carriers often store call logs and location data, making that information potentially accessible to third parties.
In both cases, you're relying on closed, outdated systems where you have almost no control.
With VoIP, you have the possibility to implement multiple layers of security to protect your calls, personal information, and sensitive customer data. That means you have control over the security of the data you want to protect.
When choosing a VoIP provider, it is important to check which security features they support. Here’s a breakdown of the security features Zadarma provides to all customers, completely free of charge.
Zadarma’s Security Features
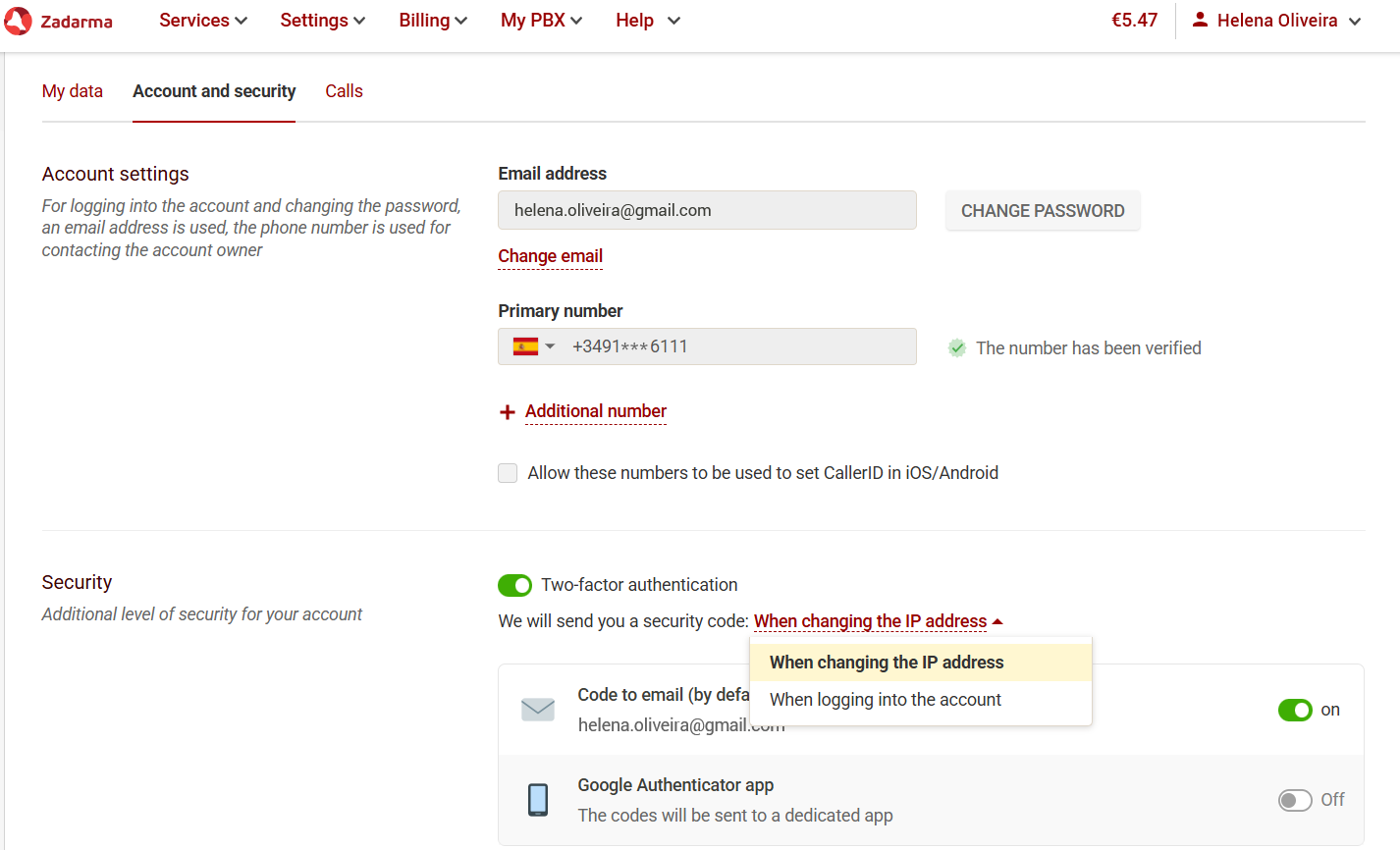
2FA authentication
In your Zadarma account, you can enable two-factor authentication (2FA). With 2FA activated, logging in requires two steps.
First, enter your email and password. Then, verify your identity using a code sent to your email or generated by the Google Authenticator app. This feature reduces the risk of unauthorized access or data breach.
TLS and SRTP encryption
Zadarma provides applications for iOS, Android, Windows, and macOS which can be used for calls and SMS messages. In all of these applications, you can enable TLS transport, which automatically activates SRTP for VoIP call encryption.
You can also make and receive calls through the web phone available in your account, or via the free Teamsale CRM. These tools use WebRTC, which provides built-in encryption.
Restriction by IP
If you’re worried about your account’s security or unauthorized calls, you can enable IP restriction in the “Settings - SIP connection” section. Or in the “My PBX - Extensions” section if you are using our free Cloud PBX. With this feature, you can specify the IP address from which calls are allowed to be made.
Calls from any other IP addresses will be blocked, and you can update the allowed IP anytime if your network changes.
Virtual Numbers for privacy protection
Use a virtual number to communicate or manage online accounts without revealing your personal phone number. Whether for business or personal use, you can have one or multiple virtual numbers for different markets, platforms, or purposes. Virtual numbers don’t require SIM cards, allowing you to use multiple numbers on a single device.
Virtual numbers can be used from any location in the world. This means that the number itself does not reveal or provide specific location data.
At Zadarma, we provide phone numbers in over 110 countries, and in 27 of them you can also receive SMS messages.
Control access to your Virtual Numbers and calls
Your Zadarma account gives you control over your virtual phone number security. You can restrict specific users from making calls, add or remove them from call queues, add business hours for incoming calls, change individual user passwords, delete users, and monitor their calling activity, from a single interface.
For added protection, you can set a price limit per minute for calls. This ensures that no calls will be made to destinations that exceed the specified cost.
Automatic email alerts
If someone connects from a country different from your usual location, you'll receive an automatic email alert. The alert will include the IP address, country, city, and time of the login attempt.
Automatic blocking for suspicious call activity
If the system detects suspicious calling behavior, such as calls to high-cost destinations or repeated calls to the same number within a short period, the account will be automatically blocked for security reasons.
To unblock the account, you will need to contact our support team and provide the necessary information. This ensures that only the account owner can unlock the account.
eSIM for secure and reliable internet connection
If you’re concerned about using public internet connections while traveling or working remotely, Zadarma has you covered. We offer eSIMs for over 150 countries, with 7 regional packages. For example, our Europe package that covers 47 countries.
This means you can use a secure internet connection on your mobile device and share it with your other devices. Protect the sensitive data stored on your devices with reliable, safe connectivity.
24/7 Customer and Technical support
If you suspect that your account may have been hacked or encounter any other issues, you can contact our support team immediately. Our team is available 24/7 to ensure your concerns are addressed promptly.
Choosing a reliable VoIP provider means getting strong security features included. Switching to VoIP isn’t just about trying something new. It’s about secure communication.
With Zadarma, you can easily protect sensitive information at no extra cost. Secure calls and data protection is no longer beyond your control.
 Calls
Calls
 Phone numbers
Phone numbers
 SMS
SMS
 Business Phone System
Business Phone System
 eSIM for Internet
eSIM for Internet
 AI agent
AI agent
 AI Speech Analytics
AI Speech Analytics
 Click to Call
Click to Call
 VoIP for Business
VoIP for Business
 Become a partner
Become a partner
 Integrations
Integrations
 For whom
For whom
 Setup guides
Setup guides
 FAQ
FAQ
 Online chat
Online chat
 Contact us
Contact us
 Blog
Blog













